People matter: trust and risk
Pushing and tripping, the boys steadily made their way to open and aggressive brawling. One of the Dads (who also happened to be a secondary school dean) tagged in as referee for the second half and was out to reshape the match from the get go. He stopped play at the first hint of ugly sportsmanship, oblivious to the objections of the individuals involved. His message was clear: “I saw what happened in the first half. I don’t care who started it, it ends here.” The boys in both teams were all good, bright kids; they got the message quick.
I thought of this moment while listening to the speakers at the August Transparency International New Zealand Leaders Integrity Forum. Andrew and Jason of the New Zealand Intelligence Community (NZIC) and Families Commissioner Len Cook discussed how effectively managing personnel could reduce the risk of fraud and corruption. Attendees at the Forum were introduced to personnel security issues by the General Manager of the Aviation Security Service, Mark Wheeler, who reflected on his dad’s advice to ‘trust no bastard’. Times, he said, had changed since his police officer dad was on the beat in the 1950s. Now, for the Aviation Security Service, it’s about managing risk while balancing that with trust.
Our Office’s 2012 fraud survey showed that many in the public sector trust their colleagues and regard their integrity as a protection against fraud and corruption risks. However, it’s important to note that trust is not a fraud control. Andrew and Jason warned that the greatest damage is often done accidentally or unintentionally and by staff and suppliers. Once, the NZIC focused almost exclusively on personnel security to protect our national interests. Nowadays, the expertise of the NZIC is available so anyone can better manage their own organisation’s personnel security risks. The Protective Security Requirements website outlines the Government’s expectations for managing personnel, physical, and information security.
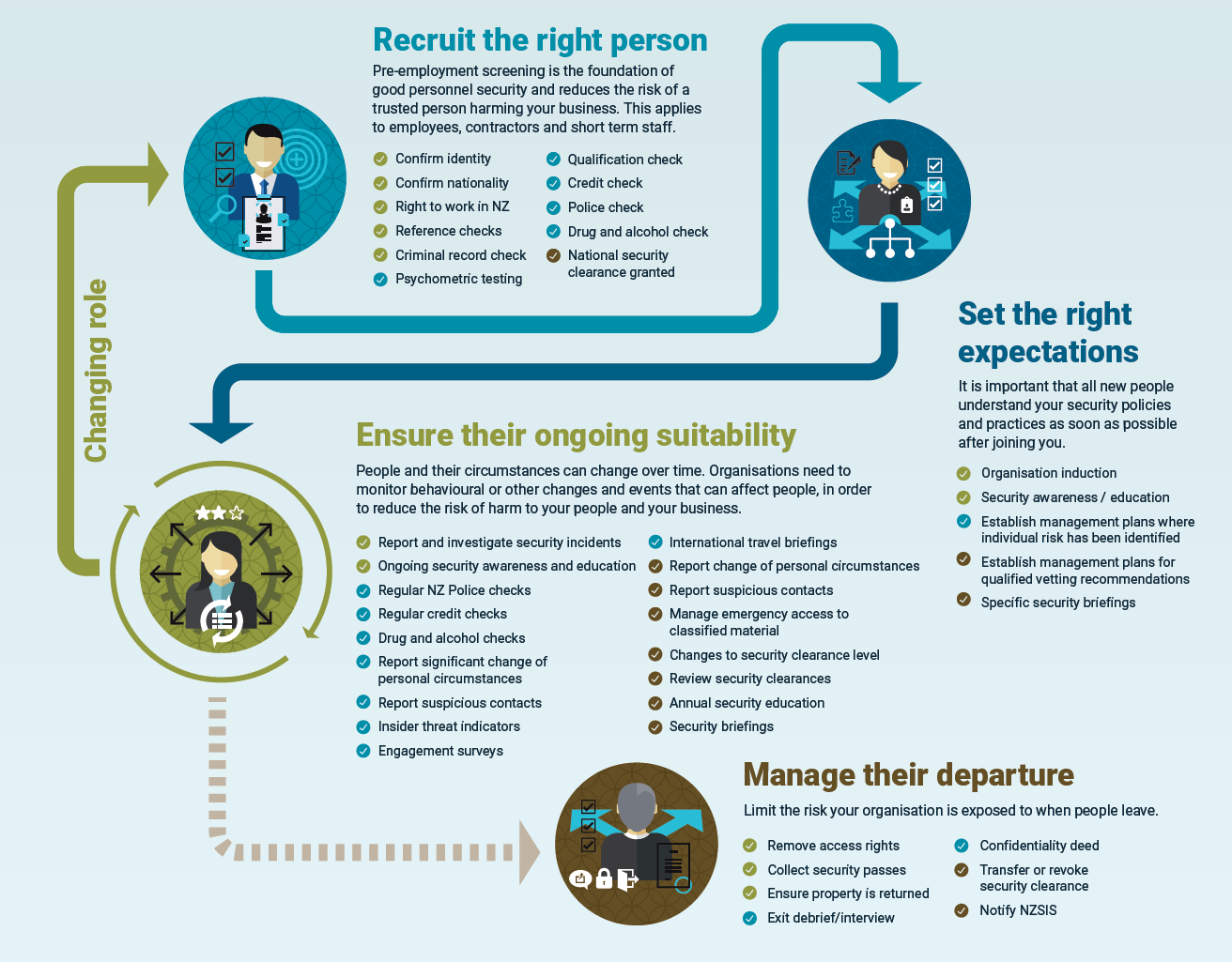
Andrew and Jason reinforced taking a risk-based approach (see the infographic below) that fits your organisational culture and context to:
- recruit the right people;
- set the right expectations;
- ensure their ongoing suitability through active management; and
- manage their departure.
It’s right for us to trust our colleagues, but we need systems and controls to protect each other, our stakeholders, our suppliers, and the public from risk. Andrew and Jason made it clear that, like the referee of my son’s football match, we need to blow the whistle quickly at the first sign of trouble. The longer that issues go without being raised and understood, the more damage they could do to everyone involved.
Len Cook then challenged us to think about our most important personnel. He described families and whānau as the undervalued but most essential partners in cultural, social, and economic progress. The public sector has a strong interest, he said, in the core business of families – that of production and reproduction. Drawing from the Social Policy Research Unit’s analysis, Len emphasised that families are the engine of public services such as health, education, and social services. But as the population ages, fewer and fewer resources will be devoted to families and to generating production.
He expressed concern that science, social policy, and public sector practices are poorly connected and that little is known about how families work. Doing so, he argued, is vital to achieving good results for all children and improving the circumstances of those most vulnerable – for example, grandparents are twice as likely to intervene in child protection situations as child protection agencies.
So we need to support families and to anticipate and understand the effect of changes in their circumstances on their ability to provide good care. In short, to think of them more like our trusted personnel.